If you want to successfully pass the Aruba Certified Network Security Associate exam, the latest HPE6-A78 dumps are indispensable.
We’ve updated HPE6-A78 dumps are the best study material for the Aruba Certified Network Security Associate exam.
Aruba-ACNSA Certifications HPE6-A78 dumps study material exam Q&A online: https://www.pass4itsure.com/hpe6-a78.html helps with exam preparation.
Do you understand the Aruba Certified Network Security Associate exam?
The Aruba Certified Network Security Associate exam has another name, the HPE6-A78 exam. For this exam, you will need to answer 60 questions in 1 hour and 30 minutes. A passing score of 63% is required. The tests are available in Japanese, English, and Latin American Spanish. Question types will have multiple choices (multiple answers) and multiple choices (single answers).
HP HPE6-A78 Exam Learning Resources:
- Aruba Network Security Fundamentals, Rev. 20.41
- Aruba Certified Network Security Associate (HPE6-A78) Study Guide
How to prepare for the HPE6-A78 exam effectively?
Perfect Pass4itSure HPE6-A78 dumps perfect for exam preparation. The newly released HP HPE6-A78 dumps are the most valuable Aruba Certified Cyber Security Assistant study material to help you pass the exam with ease.
Where can I find the most valuable Aruba Certified Cybersecurity Assistant learning materials?
Go to the Pass4itSure website. There are up-to-date HPE6-A78 dumps study materials (validated) for you to learn.
You can also download HPE6-A78 free dumps here to learn:
https://drive.google.com/file/d/1dr_G-lR0eSG8XDjhz2CWaTrVtkHTw70X/view?usp=sharing
Latest questions for Aruba Certified Network Security Associate exam
1. What is a reason to set up a packet capture on an Aruba Mobility Controller (MC)?
A. The company wants to use ClearPass Policy Manager (CPPM) to profile devices and needs to receive HTTP UserAgent strings from the MC.
B. The security team believes that a wireless endpoint connected to the MC is launching an attack and wants to examine the traffic more closely.
C. You want the MC to analyze wireless clients\\’ traffic at a lower level so that the ArubaOS firewall can control the traffic based on the application.
D. You want the MC to analyze wireless clients\\’ traffic at a lower level so that the ArubaOS firewall can control Web traffic based on the destination URL.
Correct Answer: C
2. What is an example of phishing?
A. An attacker sends TCP messages to many different ports to discover which ports are open.
B. An attacker checks a user\\’s password by using trying millions of potential passwords.
C. An attacker lures clients to connect to a software-based AP that is using a legitimate SSID.
D. An attacker sends emails posing as a service team member to get users to disclose their passwords.
Correct Answer: D
3. What is an Authorized client as defined by ArubaOS Wireless Intrusion Prevention System (WIP)?
A. a client that has a certificate issued by a trusted Certification Authority (CA)
B. a client that is not on the WIP blacklist
C. a client that has successfully authenticated to an authorized AP and passed encrypted traffic
D. is a client that is on the WIP whitelist.
Correct Answer: C
4. You need to deploy an Aruba instant AP where users can physically reach It. What are two recommended options for enhancing security for management access to the AP? (Select two)
A. Disable Its console ports
B. Place a Tamper Evident Label (TELS) over its console port
C. Disable the Web Ul.
D. Configure WPA3-Enterprise security on the AP
E. install a CA-signed certificate
Correct Answer: BE
5. What is the benefit of Opportunistic Wireless Encryption (OWE)?
A. It allows both WPA2-capable and WPA3-capable clients to authenticate to the same WPA-Personal WLAN
B. It offers more control over who can connect to the wireless network when compared with WPA2Personal
C. It allows anyone to connect but provides better protection against eavesdropping than a traditional open network
D. It provides protection for wireless clients against both honeypot APs and man-in-the-middle (MUM) attacks
Correct Answer: C
6. What distinguishes a Distributed Denial of Service (DDoS) attack from a traditional Denial of service attack (DoS)?
A. A DDoS attack originates from external devices, while a DoS attack originates from internal devices
B. A DDoS attack is launched from multiple devices, while a DoS attack is launched from a single device
C. A DoS attack targets one server, a DDoS attack targets all the clients that use a server
D. A DDoS attack targets multiple devices, while a DoS Is designed to Incapacitate only one device
Correct Answer: A
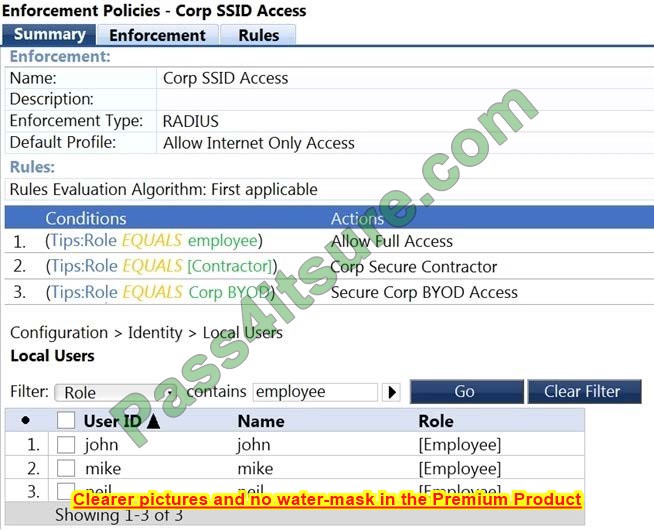
7. Refer to the exhibit.
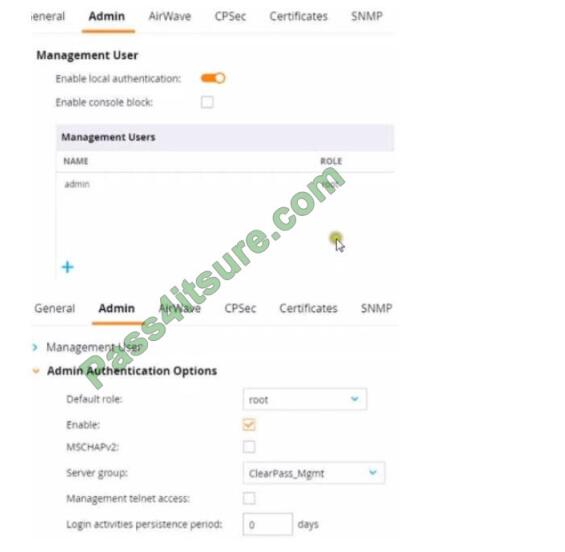
This Aruba Mobility Controller (MC) should authenticate managers who access the Web Ul to ClearPass Policy Manager (CPPM) ClearPass admins have asked you to use RADIUS and explained that the MC should accept managers\’ roles in Aruba-Admin-Role VSAs
Which setting should you change to follow Aruba’s best security practices?
A. Change the local user role to read-only
B. Clear the MSCHAP check box
C. Disable local authentication
D. Change the default role to “guest-provisioning”
Correct Answer: D
8. Refer to the exhibit.
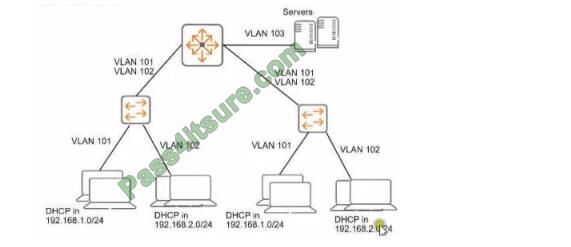
You need to ensure that only management stations in subnet 192.168.1.0/24 can access the ArubaOSSwitches\’ CLI. Web Ul. and REST interfaces The company also wants to let managers use these stations to access other parts of the network. What should you do?
A. Establish a Control Plane Policing class that selects traffic from 192.168 1.0/24.
B. Specify 192.168.1.0.255.255.255.0 as the authorized IP manager address
C. Configure the switch to listen for these protocols on OOBM only.
D. Specify VLAN 100 as the management VLAN for the switches.
Correct Answer: A
9. What is a use case for tunneling traffic between an Aruba switch and an Aruba Mobility Controller (MC)?
A. applying firewall policies and deep packet inspection to wired clients
B. enhancing the security of communications from the access layer to the core with data encryption
C. securing the network infrastructure control plane by creating a virtual out-of-band- management network
D. simplifying network infrastructure management by using the MC to push configurations to the switches
Correct Answer: A
10. What is one of the roles of the network access server (NAS) in the AAA framework?
A. It authenticates legitimate users and uses policies to determine which resources each user is allowed to access.
B. It negotiates with each user\’s device to determine which EAP method is used for authentication
C. It enforces access to network services and sends accounting information to the AAA server
D. It determines which resources authenticated users are allowed to access and monitors each users
session
Correct Answer: A
11. You have detected a Rogue AP using the Security Dashboard. Which two actions should you take in responding to this event? (Select two)
A. There is no need to locale the AP If you manually contain It.
B. This is a serious security event, so you should always contain the AP immediately regardless of your company\\’s specific policies.
C. You should receive permission before containing an AP. as this action could have legal Implications.
D. For forensic purposes, you should copy out logs with relevant information, such as the timing mat the AP was detected and the AP\\’s MAC address.
E. There is no need to locate the AP If the Aruba solution is properly configured to automatically contain it.
Correct Answer: BD
12. What is symmetric encryption?
A. It simultaneously creates ciphertext and a same-size MAC.
B. It any form of encryption mat ensures that the ciphertext Is the same length as the plaintext.
C. It uses the same key to encrypt plaintext as to decrypt the ciphertext.
D. It uses a Key that is double the size of the message that it encrypts.
Correct Answer: C
13. What is a guideline for managing local certificates on an ArubaOS-Switch?
A. Before installing the local certificate, create a trust anchor (TA) profile with the root CA certificate for the certificate that you will install
B. Install an Online Certificate Status Protocol (OCSP) certificate to simplify the process of enrolling and re-enrolling for a certificate
C. Generate the certificate signing request (CSR) with a program offline, then, install both the certificate and the private key on the switch in a single file.
D. Create a self-signed certificate online on the switch because ArubaOS-Switches do not support CA-signed certificates.
Correct Answer: C
More full HP HPE6-A78, here.
Download HPE6-A78 dumps free https://drive.google.com/file/d/1dr_G-lR0eSG8XDjhz2CWaTrVtkHTw70X/view?usp=sharing